As enterprises mature of their CI/CD journey, they have an inclination to ship code quicker, safely, and securely. One important technique the DevOps workforce applies is releasing code progressively to manufacturing, also called canary deployment. Canary deployment is a bulletproof mechanism that safely releases utility modifications and offers flexibility for enterprise experiments. It may be applied utilizing open-source software program like Argo Rollouts and Flagger. Nonetheless, superior DevOps groups wish to achieve granular management over their visitors and pod scaling whereas performing canary deployment to scale back total prices. Many enterprises obtain superior visitors administration of canary deployment at scale utilizing open-source Istio service mesh. We wish to share our data with the DevOps neighborhood via this weblog.
Earlier than we get began, allow us to focus on the canary structure applied by Argo Rollouts and Istio.
Recap of Canary Implementation Structure With Argo Rollouts and Istio
If you happen to use Istio service mesh, your whole meshed workloads could have an Envoy proxy sidecar hooked up to the applying container within the pod. You’ll be able to have an API or Istio ingress gateway to obtain incoming visitors from outdoors. In such a case, you should utilize Argo Rollouts to deal with canary deployment. Argo Rollouts offers a CRD known as Rollout to implement the canary deployment, which has similarities to a Deployment object and accountable for creating, scaling, and deleting ReplicaSets in K8s.
The canary deployment technique begins by redirecting a small quantity of visitors (5%) to the newly deployed app. Based mostly on particular standards, comparable to optimized useful resource utilization of latest canary pods, you may progressively enhance the visitors to 100%. The Istio sidecar handles the visitors for the baseline and canary as per the foundations outlined within the Digital Service useful resource. Since Argo Rollouts offers native integration with Istio, it might override the Digital Service useful resource to extend the visitors to the canary pods.
Canary could be applied utilizing two strategies: deploying new modifications as a service or deploying new modifications as a subset.
1. Deploying New Modifications as a Service
On this methodology, we will create a brand new service (known as canary) and break up the visitors from the Istio ingress gateway between the steady and canary companies. Confer with the picture beneath.
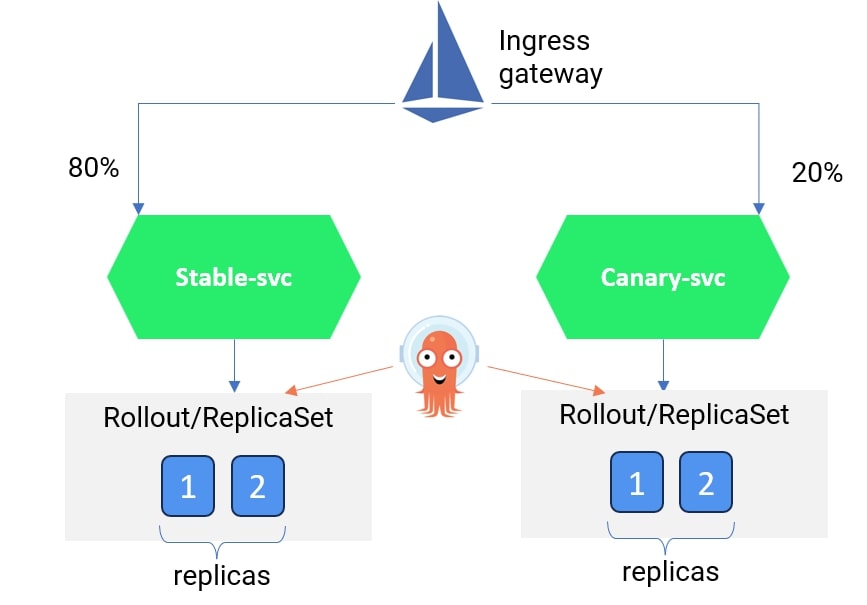
You’ll be able to check with the YAML file for a pattern implementation of deploying a canary with a number of companies right here. We now have created two companies known as rollouts-demo-stable and rollouts-demo-canary. Every service will hearken to HTTP visitors for the Argo Rollout useful resource known as rollouts-demo. Within the rollouts-demo YAML, we’ve specified the Istio digital service useful resource and the logic to progressively enhance the visitors weightage from 20% to 40%, 60%, 80%, and finally 100%.
2. Deploying New Modifications as a Subset
On this methodology, you may have one service however create a brand new Deployment subset (canary model) pointing to the identical service. Site visitors could be break up between the steady and canary deployment units utilizing Istio Digital service and Vacation spot rule sources.
Please notice that we’ve totally mentioned the second methodology on this weblog.
Implementing Canary Utilizing Istio and Argo Rollouts With out Altering Deployment Useful resource
Since there’s a misunderstanding amongst DevOps professionals that Argo Rollouts is a substitute for Deployment useful resource, and the companies thought-about for canary deployment should check with the Argo Rollouts with Deployment configuration rewritten.
Properly, that’s not true.
The Argo Rollout useful resource offers a piece known as workloadRef the place current Deployments could be referred to with out making important modifications to Deployment or service YAML.
If you happen to use the Deployments useful resource for a service in Kubernetes, you may present a reference within the Rollout CRD, after which Argo Rollouts will handle the ReplicaSet for that service. Confer with the picture beneath.
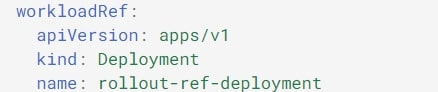
We are going to use the identical idea to deploy a canary model utilizing the second methodology: deploying new modifications utilizing a Deployment.
Argo Rollouts Configuration for Deploying New Modifications Utilizing a Subset
For instance you have got a Kubernetes service known as rollout-demo-svc and a deployment useful resource known as rollouts-demo-deployment (code beneath). You could comply with the three steps to configure the canary deployment.
Code for Service.yaml:
apiVersion: v1
sort: Service
metadata:
identify: rollouts-demo-svc
namespace: istio-argo-rollouts
spec:
ports:
- port: 80
targetPort: http
protocol: TCP
identify: http
selector:
app: rollouts-demoCode for deployment.yaml:
apiVersion: apps/v1
sort: Deployment
metadata:
identify: rollouts-demo-deployment
namespace: istio-argo-rollouts
spec:
replicas: 0 # this must be made 0 as soon as Argo rollout is energetic and purposeful.
selector:
matchLabels:
app: rollouts-demo
template:
metadata:
labels:
app: rollouts-demo
spec:
containers:
- identify: rollouts-demo
picture: argoproj/rollouts-demo:blue
ports:
- identify: http
containerPort: 8080
sources:
requests:
reminiscence: 32Mi
cpu: 5mStep 1: Setup Digital Service and Vacation spot Rule in Istio
Arrange the digital service by specifying the back-end vacation spot for the HTTP visitors from the Istio gateway. In our digital service rollouts-demo-vs2, we talked about the back-end service as rollouts-demo-svc, however we created two subsets (steady and canary) for the respective deployment units. We now have set the visitors weightage rule in order that 100% of the visitors goes to the steady model and 0% goes to the canary model.
As Istio is accountable for the visitors break up, we’ll see how Argo updates this Digital service useful resource with the brand new visitors configuration specified within the canary specification.
apiVersion: networking.istio.io/v1alpha3
sort: VirtualService
metadata:
identify: rollouts-demo-vs2
namespace: istio-argo-rollouts
spec:
gateways:
- istio-system/rollouts-demo-gateway
hosts:
- "*"
http:
- identify: route-one
route:
- vacation spot:
host: rollouts-demo-svc
port:
quantity: 80
subset: steady
weight: 100
- vacation spot:
host: rollouts-demo-svc
port:
quantity: 80
subset: canary
weight: 0Now, we’ve to outline the subsets within the Vacation spot guidelines. Within the rollout-destrule beneath, we’ve outlined the subsets canary and steady and referred to the Argo Rollout useful resource known as rollouts-demo.
apiVersion: networking.istio.io/v1alpha3
sort: DestinationRule
metadata:
identify: rollout-destrule
namespace: istio-argo-rollouts
spec:
host: rollouts-demo-svc
subsets:
- identify: canary # referenced in canary.trafficRouting.istio.destinationRule.canarySubsetName
labels: # labels shall be injected with canary rollouts-pod-template-hash worth
app: rollouts-demo
- identify: steady # referenced in canary.trafficRouting.istio.destinationRule.stableSubsetName
labels: # labels shall be injected with steady rollouts-pod-template-hash worth
app: rollouts-demoWithin the subsequent step, we’ll arrange the Argo Rollout useful resource.
Step 2: Setup Argo Rollout Useful resource
The rollout spec ought to notice two vital gadgets within the canary technique: declare the Istio digital service and vacation spot rule and supply the visitors increment technique.
You’ll be able to study extra concerning the Argo Rollout spec.
In our Argo rollout useful resource, rollouts-demo, we’ve supplied the deployment (rollouts-demo-deployment) within the workloadRef spec. Within the canary spec, we’ve referred to the digital useful resource (rollouts-demo-vs2) and vacation spot rule (rollout-destrule) created within the earlier step.
We now have additionally specified the visitors guidelines to redirect 20% of the visitors to the canary pods after which pause for guide route.
We now have given this guide pause in order that within the manufacturing setting, the Ops workforce can confirm whether or not all of the important metrics and KPIs, comparable to CPU, reminiscence, latency, and the throughput of the canary pods, are in an appropriate vary.
As soon as we manually promote the discharge, the canary pod visitors will enhance to 40%. We are going to wait 10 seconds earlier than rising the visitors to 60%. The method will proceed till the visitors to the canary pods will increase to 100% and the steady pods are deleted.
apiVersion: argoproj.io/v1alpha1
sort: Rollout
metadata:
identify: rollouts-demo
namespace: istio-argo-rollouts
spec:
replicas: 5
technique:
canary:
trafficRouting:
istio:
virtualService:
identify: rollouts-demo-vs2 # required
routes:
- route-one # optionally available if there's a single route in VirtualService, required in any other case
destinationRule:
identify: rollout-destrule # required
canarySubsetName: canary # required
stableSubsetName: steady # required
steps:
- setWeight: 20
- pause: {}
- setWeight: 40
- pause: {length: 10}
- setWeight: 60
- pause: {length: 10}
- setWeight: 80
- pause: {length: 10}
revisionHistoryLimit: 2
selector:
matchLabels:
app: rollouts-demo
workloadRef:
apiVersion: apps/v1
sort: Deployment
identify: rollouts-demo-deploymentAfter you have deployed all of the sources in steps 1 and a couple of and accessed them via the Istio ingress IP from the browser, you will notice an output just like the one beneath.

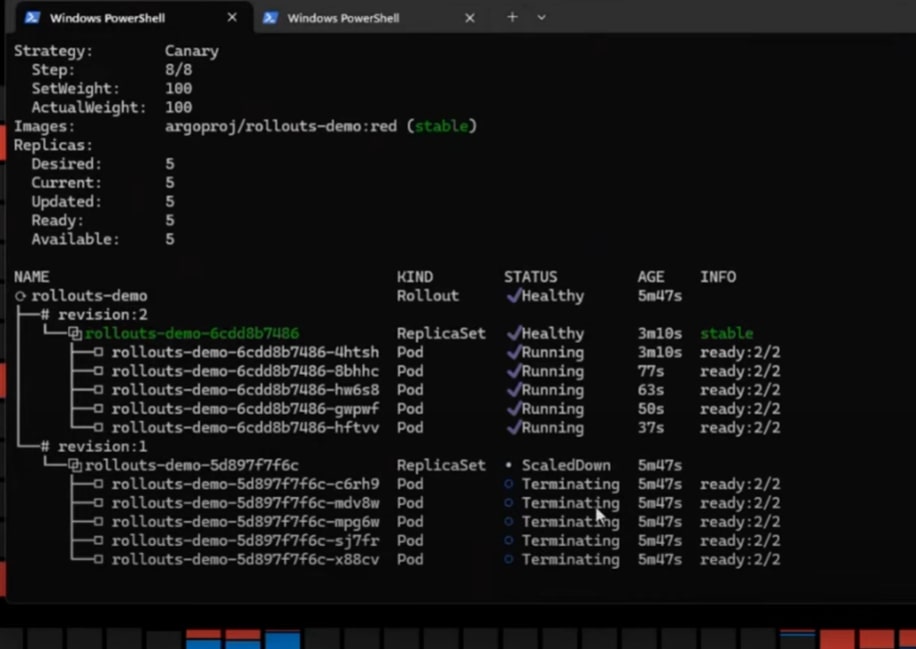
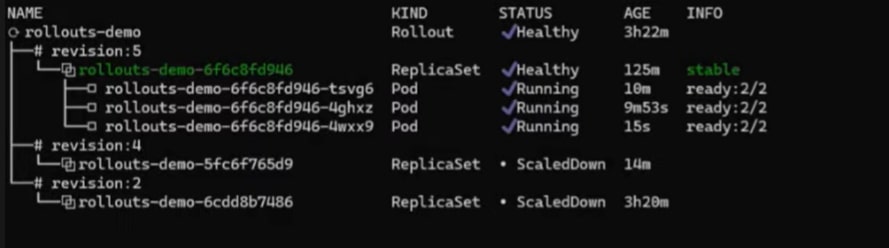
You’ll be able to run the command beneath to know how the pods are dealt with by Argo Rollouts.
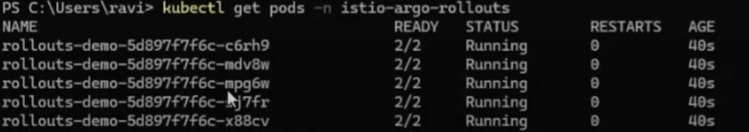
Validating Canary Deployment
Let’s say builders have made new modifications and created a brand new picture that’s alleged to be examined. For our case, we’ll make the Deployment manifest file (rollouts-demo-deployment) by modifying the picture worth from blue to purple (check with the picture beneath).
spec:
containers:
- identify: rollouts-demo
picture: argoproj/rollouts-demo:blueWhen you deploy the rollouts-demo-deployment, Argo Rollout will perceive that new modifications have been launched to the setting. It might then begin making new canary pods and permit 20% of the visitors. Confer with the picture beneath:
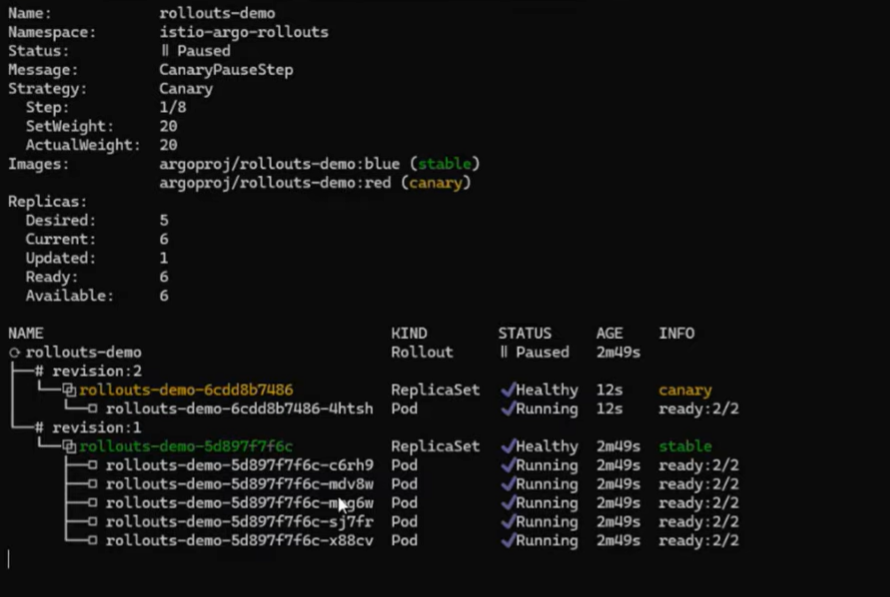
Now, for those who analyze the digital service spec by working the next command, you’ll understand Argo has up to date the visitors share to canary from 0% to twenty% (as per the Rollouts spec).
kubectl get vs rollouts-demo-vs2 -n > -o yaml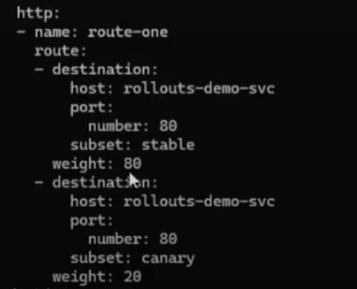
Step by step, 100% of the visitors shall be shifted to the brand new model, and older/steady pods shall be terminated.
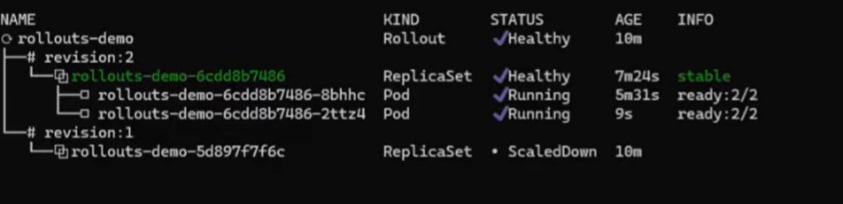
In superior instances, the DevOps workforce should management the scaling of canary pods. The concept is to not create all of the pods as per the duplicate at every gradual shifting of the canary however to create the variety of pods primarily based on particular standards. In these instances, we’d like HorizontalPodAutoscaler (HPA) to deal with the scaling of canary pods.
Scaling of Pods Throughout Canary Deployment Utilizing HPA
Kubernetes HPA is used to extend or lower pods primarily based on load. HPA will also be used to regulate the scaling of pods throughout canary deployment. HorizontalPosAutoscaler overrides the Rollouts habits for scaling of pods.
We now have created and deployed the next HPA useful resource: hpa-rollout-example.
- Observe: The HPA will create the variety of pods = most (minimal pods as per HPA useful resource, or variety of the replicas talked about within the
Rollouts).
This implies if the variety of pods talked about within the HPA useful resource is 2 however the replicas as per the Rollouts useful resource is 5, then a complete of 5 pods shall be created.
Equally, if we replace the replicas within the rollouts-demo useful resource as 1, then the variety of pods created by HPA shall be 2. (We could have up to date the replicas to 1 to check this state of affairs.)
Within the HPA useful resource, we’ve referenced the Argo Rollout useful resource rollouts-demo. Which means HPA shall be accountable for creating two replicas at the beginning. If the CPU utilization is greater than 10%, extra pods shall be created. A most of six replicas shall be created.
apiVersion: autoscaling/v1
sort: HorizontalPodAutoscaler
metadata:
identify: hpa-rollout-example
namespace: istio-argo-rollouts
spec:
maxReplicas: 6
minReplicas: 2
scaleTargetRef:
apiVersion: argoproj.io/v1alpha1
sort: Rollout
identify: rollouts-demo
targetCPUUtilizationPercentage: 10After we deployed a canary, solely two replicas had been created at first (as a substitute of the 5 talked about within the Rollouts).
Validating Scaling of Pods by HPA by Rising Artificial Masses
We are able to run the next command to extend the masses to a sure pod.
kubectl run -i -tty load-generator-1 -rm -image=busybox:1.28 -restart=By no means - /bin/sh -c "while sleep 0.01; do wget -q -O- http://>.>; done;"You employ the next command to look at the CPU utilization of the pods created by HPA.
kubectl get hpa hpa-rollout-example -n > -watchAs soon as the load will increase greater than 10%, in our case to 14% (check with the picture beneath), new pods shall be created.
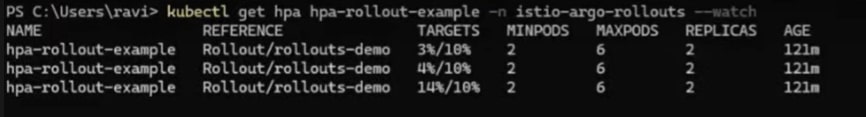
 Many metrics, comparable to latency or throughput, can be utilized by HPA as standards for scaling up or down the pods.
Many metrics, comparable to latency or throughput, can be utilized by HPA as standards for scaling up or down the pods.
Video
Beneath is the video by Ravi Verma, CTO of IMESH, giving a walkthrough on superior visitors administration in Canary for enterprises at scale utilizing Istio and Argo Rollouts.
Closing Thought
Because the tempo of releasing software program will increase with the maturity of the CI/CD course of, new problems will emerge. And so will new necessities by the DevOps workforce to sort out these challenges. Equally, when the DevOps workforce adopts the canary deployment technique, new scale, and visitors administration challenges emerge to achieve granular management over the speedy launch course of and infrastructure value.

