Securing data is essential as cyber-attacks are getting extra subtle. Information residing in an unprotected state at relaxation (databases, saved information, and backups) pose one of the vital dangers.
Information at relaxation encryption is critical to ensure that data is protected and unreadable even within the occasion of unlawful entry. This dialogue highlights why encrypting knowledge is seen as an indispensable a part of bolstering general cyber safety and protecting belongings protected from undesirable entry.
Deciphering Dormant Information
Not like knowledge in transit, the place knowledge is repeatedly shifting between techniques and over networks, knowledge at relaxation refers to data that exists on a chunk of {hardware} or inside any digital storage system.
Their backup techniques have a wholly totally different set of safety challenges to maintain out malicious actors versus knowledge in transit that’s protected via well-defined protocols throughout motion.
Picture Supply
Examples of information at relaxation embrace information on onerous drives, structured organized teams of data (together with database tables), and archived backups. This knowledge might be accessible via alternate apps or interfaces which can be static.
Varonis’s World in Information Breaches report said that 7 million unencrypted knowledge data are compromised day by day. Information at relaxation is necessary in some sectors reminiscent of healthcare and finance. This ensures that it meets relevant laws like HIPAA, offering safety to healthcare business knowledge. It additionally secures personal monetary data in finance towards theft and illegal use.
Authorities entities make use of robust encryption to safeguard confidential data and forestall unlawful entry. Information at relaxation safety stays a linchpin to a full spectrum of cyber safety.
The Rising Risk Panorama
A urgent situation in cybersecurity developments is the rising array of high-level assaults being aimed straight at knowledge at relaxation. A few of these applied sciences are at the moment being utilized by hackers.
Malicious actors can encrypt the victims’ knowledge and maintain it for ransom thus denying them entry, or promote confidential data. Moreover, social engineering assaults are sometimes employed to trick people into revealing delicate data or credentials. Within the case of ineffective data-at-rest encryption, these assaults may end up in a large-scale breach that places personal data organizations in danger.
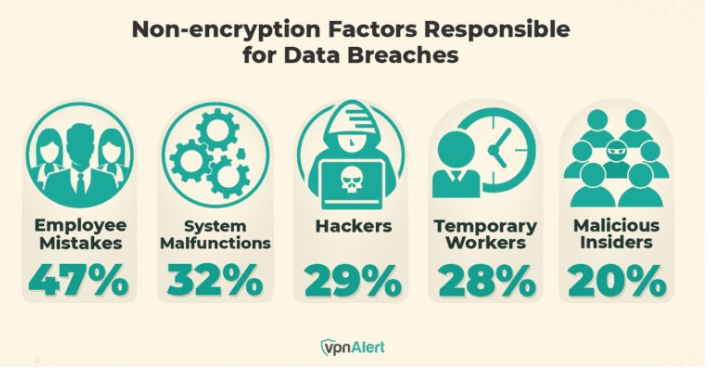
Picture Supply
The hazards linked to unprotected knowledge at relaxation are sharply dropped at mild by the Capital One knowledge breach of 2019. On this incident, greater than 100 million private particulars of the financial institution’s shoppers had been leaked when a hacker breached the establishment’s cloud-stored knowledge as a consequence of a misconfigured firewall. The assault’s affect might have been considerably decreased by stronger knowledge storage encryption that may make the stolen data nugatory with out the decryption key.
The repercussions of information at relaxation compromise are catastrophic; companies could expertise monetary losses straight via fines and authorized charges and not directly via damaging model recognition and lack of shopper belief.
Moreover, as the method of recovering after such hacking usually entails expensive implementations of latest safety techniques and processes, the implications for a corporation’s day by day functioning in the long run are extreme. Any enterprise that seeks to defend its most significant property from an escalating hazard profile should begin implementing data-at-rest encryption in the present day. That is now not an possibility.
How Information at Relaxation Encryption Works
Shielding inactive knowledge saved on bodily units reminiscent of onerous drives, databases, or cloud storage requires data-at-rest encryption. It ensures that nobody can learn or profit from this saved knowledge when uncovered to illicit attain with out appropriate encryption keys. That is the way it works:
A. Encryption Algorithms
Two fundamental algorithms are employed in encrypting saved knowledge. They’re:
Symmetric Encryption
This system makes use of a single key for each encryption and decryption. It’s a quick strategy and useful for giant datasets. However the issue lies in sharing the important thing between events safely.
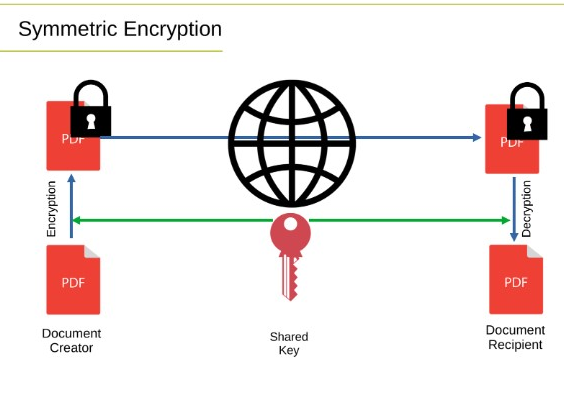
Picture Supply
Uneven Encryption
This encryption method makes use of two keys, the general public key to encrypt and the personal key to decrypt. This technique improves safety by eliminating secret keys that must be shared although it’s slower.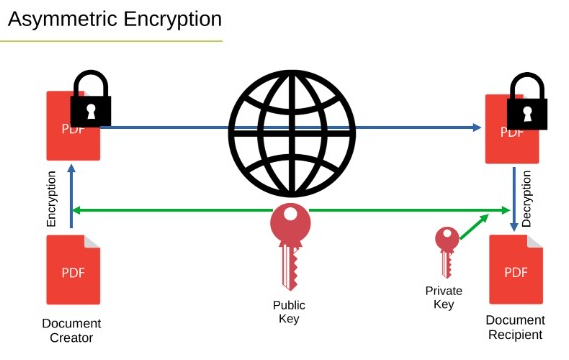
Picture Supply
B. Encryption Keys
Saved knowledge encryption safety is extra depending on the protection of the entry keys. Robust key administration processes reminiscent of safe storage, rotation, and entry management are required to be in place. Key safety ensures the info stays ineffective even when encrypted knowledge is stolen.
The very best password managers are among the many best key safety additions you may make. It’s useful to have these instruments and aid you retailer the keys securely guaranteeing that none aside from licensed personnel can entry them.
C. Implementing Encryption
Information at relaxation is encrypted utilizing two fundamental strategies: Software program-Primarily based Encryption and {Hardware}-Primarily based Encryption.
Software program-based encryption means specialised software program used to save lots of knowledge to any gadget. This sort of knowledge encryption is customizable and could also be used for varied storage techniques. Nevertheless, software-based encryption techniques require processor energy to encrypt knowledge themselves, which could elevate latency and system points.
The second kind is hardware-based encryption, constructed into {hardware} storage itself. This system encrypts and decrypts data extra shortly and calls for fewer system sources. Self-encrypting drives is an instance.
Regulatory Compliance and Information Safety Legal guidelines
Certainly, compliance and knowledge safety are essential. Requirements reminiscent of GDPR(Common Information Safety Regulation) and HIPAA (Well being Insurance coverage Portability and Accountability Act), have made the safety of delicate data an integral half. These legal guidelines dictate robust knowledge safety measures for private and well being data.
Information at relaxation encryption is important to make sure compliance with these mandates. When knowledge is encrypted at relaxation, companies can safe their saved knowledge in case of a breach the place unauthorized entry has been correctly managed. This helps preserve delicate knowledge inaccessible to anybody with out the suitable decryption keys, and due to this fact compliant with GDPR privateness guidelines and HIPAA protections for private well being data.
Encryption is employed by 42% of respondents for buyer knowledge, rating it because the fifth mostly encrypted kind of knowledge in companies. Implementing knowledge at storage encryption helps in regulation and most significantly the belief of shoppers.
Companies can strengthen buyer relationships by investing in defending private data. On the similar time, robust safety techniques stop fines and authorized points because of knowledge leaks, finally saving organizations from monetary losses and reputational injury.
Integrating Information at Relaxation Encryption right into a Complete Safety Technique
Static knowledge encryption matches seamlessly right into a defense-in-depth technique by offering an extra layer of safety. Whereas firewalls and intrusion detection techniques (IDS) safeguard towards unapproved community entry and monitor suspicious exercise, encryption ensures that even when these shields are breached, the info stays inaccessible. Encrypting knowledge at relaxation provides an important safeguard, rendering stolen or intercepted knowledge unreadable with out the correct decryption keys.
Encryption enhances firewalls, IDS, and multi-factor authentication (MFA). Firewalls shield towards unsanctioned entry from the skin, and IDS detects and alerts customers to potential threats, whereas MFA gives extra identification authentication for consumer account entry. Blockchain expertise additional enhances this safety framework by providing a decentralized ledger that ensures knowledge integrity and transparency, making it almost not possible for unauthorized events to change data.
Combining them is a holistic safety resolution. Subsequently, encryption retains any data intercepted protected; firewalls and IDSs then again assist safe the info from being accessed or exploited within the first place.
Saved knowledge encryption mixed with different safety elements strengthens general knowledge safety thereby minimizing danger. It constructs a whole resolution for exterior assaults and inside knowledge safety offering full-fledged safety towards normal threats or potential inside jobs. Embedding encryption into a bigger safety technique creates an adaptable safeguard that narrows the assault floor and strengthens knowledge towards many varieties of threats.
Securing the Basis of Information Safety With Encryption
On this period of rising cyber threats and knowledge breaches, encrypting knowledge at relaxation is a vital additional layer of protection. Encrypting at relaxation secures saved knowledge by defending towards unauthorized entry offering improved security, compliance, and privateness of the info.
Because of growing cyber threats, it’s changing into more and more needed moderately than non-compulsory for organizations to determine themselves with encryption options to safe their belongings and keep confidence throughout the digital realm.

