Just lately in one among my tasks, there was a requirement to create JWT inside the MuleSoft utility and ship that as an OAuth token to the backend for authentication. After doing a little analysis, I acquired to know a number of methods to create JWT like Java code, DataWeave code, JWT signal module, and so on. Java code could be complicated to implement, Dataweave code doesn’t work for the RSA algorithm and the shopper didn’t wish to use a customized module just like the JWT signal module. Lastly, I acquired to know in regards to the DataWeave JWT Library accessible in MuleSoft Alternate.
On this weblog, I might be describing the method of making JWT utilizing the Dataweave JWT Library accessible in Mulesoft Alternate which helps each HMAC and RSA algorithms.
Background
JSON Net Token
JSON Net Token (JWT) is an open normal that gives a mechanism for securely transmitting knowledge between events as a JSON object. JWTs are comparatively smaller in dimension and due to that they are often despatched by a URL, POST parameter, or HTTP header, and it’s transmitted shortly.
JSON Net Token Construction
JSON Net Tokens are product of three components separated by dots (.), that are:
1. Header
The primary half is the Base64-URL encoded header which generally consists of two fields: the kind of the token, which is JWT, and the signing algorithm getting used (HMAC or RSA).
For instance:
{
"alg": "RS256",
"typ": "JWT"
}2. Payload
The second a part of the token is the payload, that are Base64-URL encoded claims. Claims are particulars in regards to the person and a few extra knowledge.
For instance:
{
"sub": "jwt-demo@test.com",
"aud": "https://test.mulesoft.com",
"exp": "1661508617"
}Please word that for signed tokens, this info is protected towards tampering, however it’s readable by anybody. Don’t put delicate info within the payload or header components of a JWT except it’s encrypted.
3. Signature
To create the signature half we have to take the Base64-URL encoded header, the Base64-URL encoded payload, a personal key or secret key primarily based on the algorithm sort (HMAC or RSA), and the algorithm specified within the header, and signal that.
- Within the case of an HMAC signature, a secret secret’s used to signal the JWT by the shopper, and the identical secret secret’s used to validate the JWT by the server.
- Within the case of an RSA signature, the personal secret’s used to signal the JWT by the shopper, and the general public secret’s used to validate the JWT by the server. This ensures that the message is just not modified alongside the best way and that the sender of the JWT is who it says it’s.
Under is an instance of JWT for the above-encoded header and payload, which is signed with a personal key:
eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiJqd3QtZGVtb0B0ZXN0LmNvbSIsImF1ZCI6Imh0dHBzOi8vdGVzdC5tdWxlc29mdC5jb20iLCJleHAiOjE2NjE1MDg2MTd9.WnXOmrIv2SRF940x5qGuiRUkPJ14rBMnDRc53NLCf8LbJXEiwiSlKaulQGwRwBsBBG1C2DcANVqabC1KkeCen5D1dKaaabGo8BtV83qiP9FyKIhRgl81ldzOZ0QuybqBF78-Tq8LpjAX6W4HIlU5Im6MhgARnWKillxPbnwK8t_AVxIFxl2JW_h0gNbqT9tnOR2YDFm3gNlfLvHEu01FgI8LW9VQLvEuCsEMSCaz7-t1JsQ9nH8wGoVnmU0NgCyRBMd3F0hoCDzIP1PMJSceOHVdlK4hsmsjmDLsVUT0aInhoWqeyVcJkoULmBB34VUazV0yjXLzup26jUvfFxkwlA
Walkthrough
Step 1
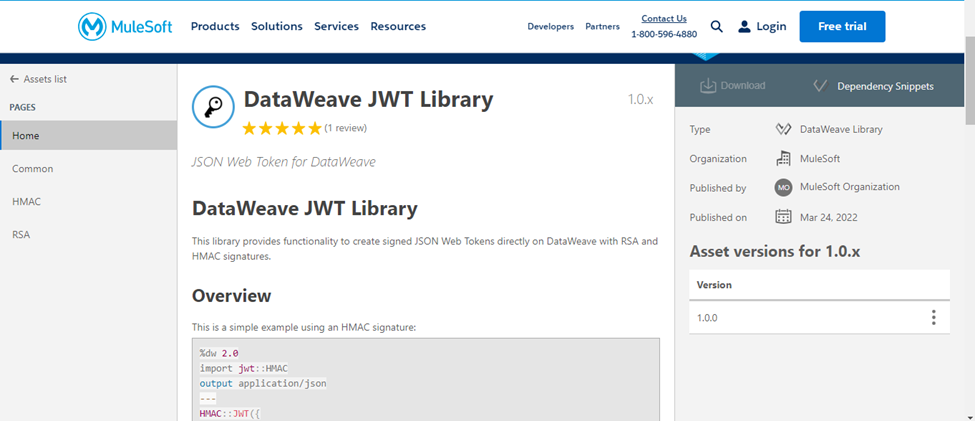
Go to Dataweave JWT Library in MuleSoft Alternate.
Step 2
Copy the dependency snippet from the Alternate and add it to your mission’s pom.xml dependencies part.
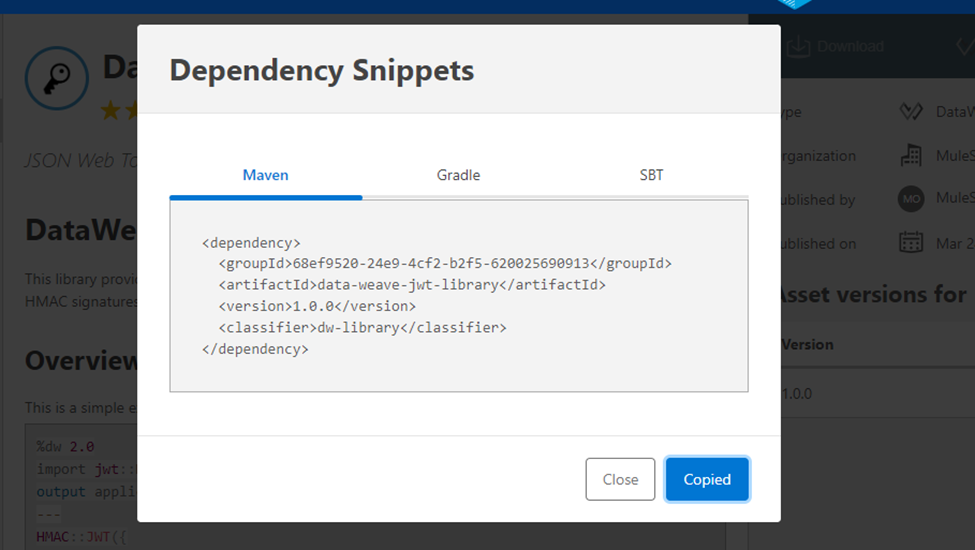
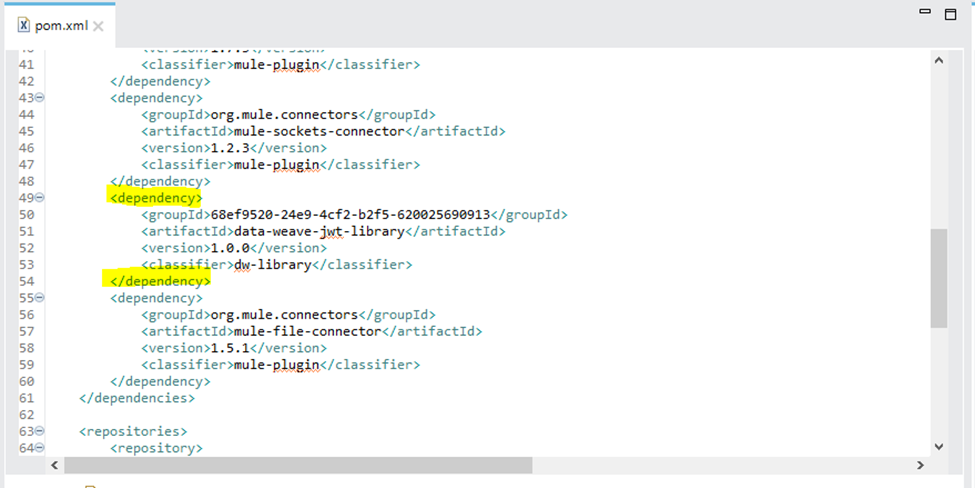
This may import the Dataweave JWT Library from MuleSoft Alternate to your MuleSoft utility.
Step 3
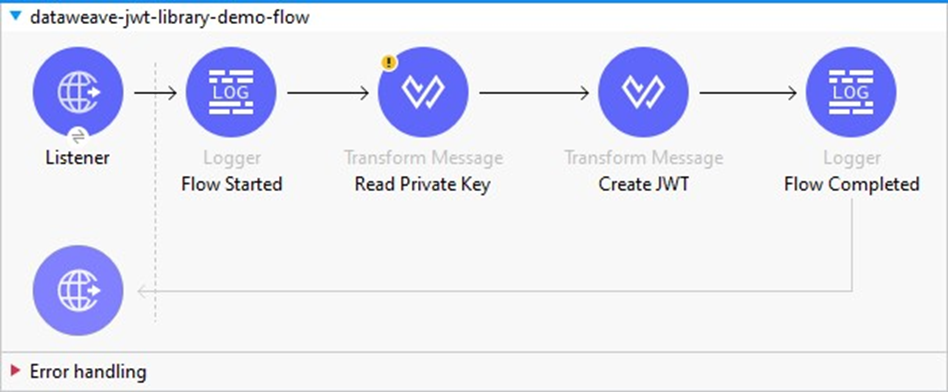
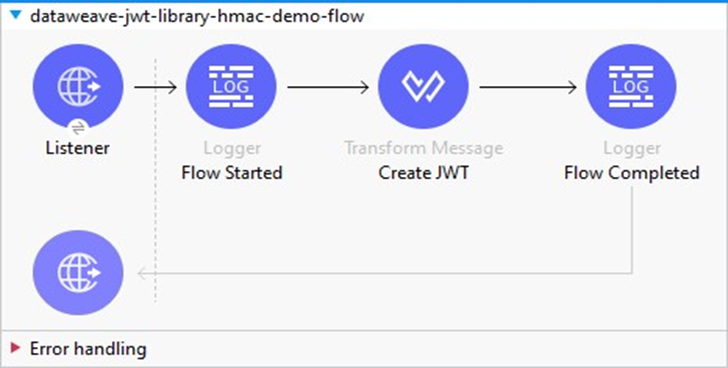
Add a remodel message in your stream to create JWT.
Create JWT With RSA Algorithm
- Step 1: Add the remodel message to learn the personal key within the Mule utility and retailer it in a variable.
output utility/json
---
readUrl("classpath://pkcs1-rsa256-privatekey.pem","text/plain") substitute "r" with ""Right here, the personal secret’s current underneath the src/fundamental/sources folder and we’re studying the personal key into Mule stream utilizing the DataWeave readUrl operate. You may as well load the personal key utilizing the file learn connector or some other method like loading from Azure Key Vault, AWS Secret Supervisor, and so on. as per use case requirement. Additionally, it’s essential test the brand new line character in your personal key. Whether it is “rn” as a substitute of “n” then we have to take away the additional “r” like above. The JWT library helps personal keys with the brand new line character “n”.
- Step 2: Add the remodel message to create the JWT.
Right here, we have to move the 4 parameters under to the JWT operate.
| Sr. No | Parameter | Datatype | Description | Instance |
|---|---|---|---|---|
|
1 |
header |
Object |
JWT Header |
|
|
2 |
payload |
Object |
JWT Payload |
|
|
3 |
key |
String |
RSA personal keys. |
|
|
4 |
algorithm |
String |
The supported RSA algorithms are:
|
Sha256withRSA |
DataWeave:
%dw 2.0
import * from jwt::RSA
output utility/json
---
{
token: JWT(
{
"alg": "RS256",
"typ": "JWT"
},
{
iss: "jwt-rsa-demo@test.com",
aud: 'https://check.mulesoft.com',
iat: (now()) as Quantity { unit: 'seconds' },
exp: (now() + |PT7200S|) as Quantity { unit: 'seconds' }
},
vars.privateKey as String,
'Sha256withRSA'
),
expiration: (now() + |PT7150S|)
}Create JWT With HMAC Algorithm
- Step 1: Add the remodel message to create the JWT.
Right here, we have to move the 4 parameters under to the JWT operate.
| Sr. No. | Parameter | Datatype | Description | Instance |
|---|---|---|---|---|
|
1 |
header |
Object |
JWT Header |
|
|
2 |
payload |
Object |
JWT Payload |
|
|
3 |
signingKey |
String |
Secret Key |
|
|
4 |
algorithm |
String |
The supported HMAC algorithms are:
|
|
DataWeave:
%dw 2.0
import * from jwt::HMAC
output utility/json
var secretKey = "MuleJWTPassword@2023"
---
{
token: JWT(
{
"alg": "HS256",
"typ": "JWT"
},
{
iss: "jwt-hmac-demo@test.com",
aud: 'https://check.mulesoft.com',
iat: (now()) as Quantity { unit: 'seconds' },
exp: (now() + |PT7200S|) as Quantity { unit: 'seconds' }
},
secretKey as String,
'HmacSHA256'
),
expiration: (now() + |PT7150S|)
}Step 4
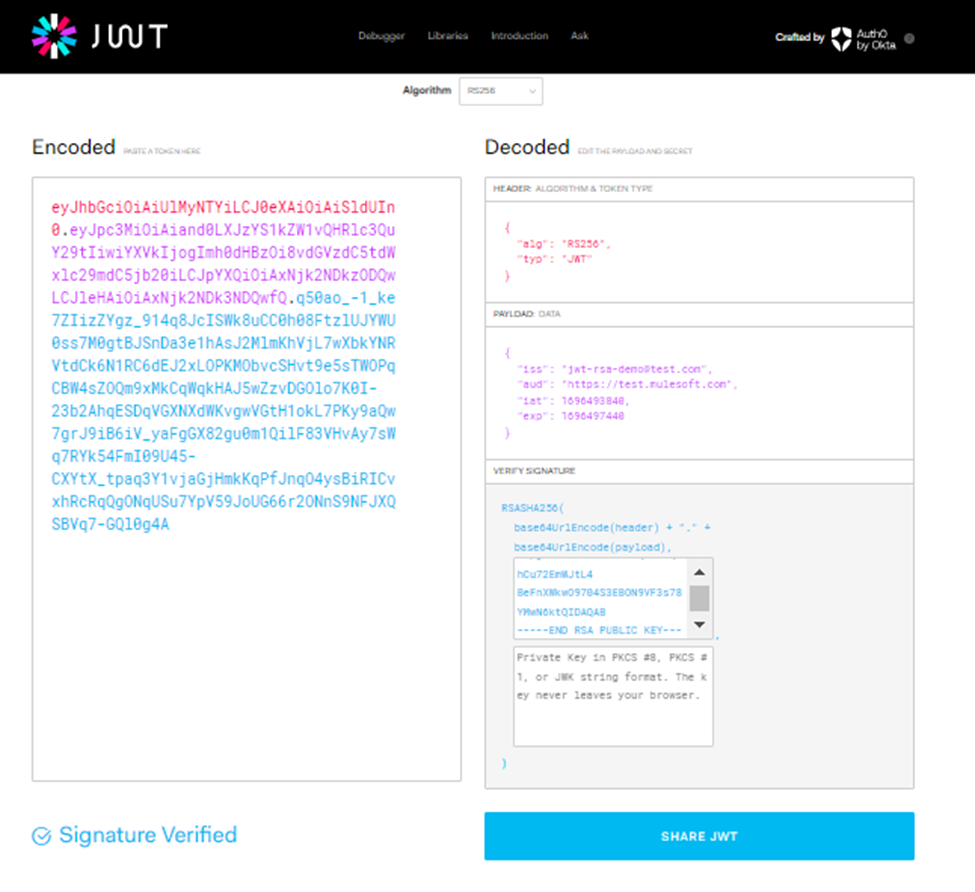
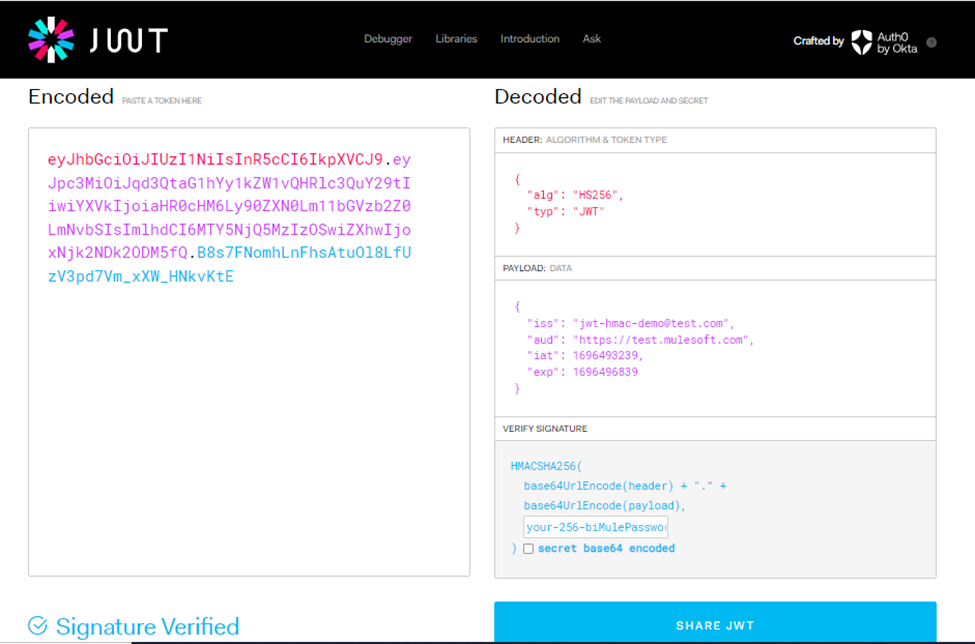
Set off the request and it’ll generate JWT.
{
"token": "eyJhbGciOiAiUlMyNTYiLCJ0eXAiOiAiSldUIn0.eyJpc3MiOiAiand0LXJzYS1kZW1vQHRlc3QuY29tIiwiYXVkIjogImh0dHBzOi8vdGVzdC5tdWxlc29mdC5jb20iLCJpYXQiOiAxNjk2NDkzODQwLCJleHAiOiAxNjk2NDk3NDQwfQ.q50ao_-1_ke7ZIizZYgz_914q8JcISWk8uCC0h08FtzlUJYWU0ss7M0gtBJSnDa3e1hAsJ2MlmKhVjL7wXbkYNRVtdCk6N1RC6dEJ2xLOPKMObvcSHvt9e5sTWOPqCBW4sZOQm9xMkCqWqkHAJ5wZzvDGOlo7K0I-23b2AhqESDqVGXNXdWKvgwVGtH1okL7PKy9aQw7grJ9iB6iV_yaFgGX82gu0m1QilF83VHvAy7sWq7RYk54FmI09U45-CXYtX_tpaq3Y1vjaGjHmkKqPfJnqO4ysBiRICvxhRcRqQgONqUSu7YpV59JoUG66r2ONnS9NFJXQSBVq7-GQl0g4A",
"expiration": "2023-10-05T14:46:30.505+05:30"
}{
"token": "eyJhbGciOiAiSFMyNTYiLCJ0eXAiOiAiSldUIn0.eyJpc3MiOiAiand0LWhtYWMtZGVtb0B0ZXN0LmNvbSIsImF1ZCI6ICJodHRwczovL3Rlc3QubXVsZXNvZnQuY29tIiwiaWF0IjogMTY5NjQ5MzIzOSwiZXhwIjogMTY5NjQ5NjgzOX0.sAiK-Bto_8JS4WLJa3nFoSYCIIv3IiXYLyL0QKXB-hQ",
"expiration": "2023-10-05T14:36:29.62+05:30"
}Validation
- Validate RSA JWT utilizing public key:
 Validate HMAC JWT utilizing a secret key:
Validate HMAC JWT utilizing a secret key:
Limitations
DataWeave JWT Library doesn’t assist encrypted personal keys to generate JWT utilizing the RSA algorithm. If the requirement is to create JWT utilizing the RSA algorithm with an encrypted personal key, you should use both customized Java code or JWT Signal Module.

